Imagine running critical business operations on software from decades ago, no updates, no support, just mounting risks. Surprisingly, many companies do just that with legacy systems. This leads us to the fundamental question: what is end of life software?
This blog will answer that question, explain the dangers of EOL software, and how to manage it. We’ll clarify the difference between EOL and End of Support (EOS), provide best practices, and offer strategies to minimize risks.
Effective software lifecycle management is crucial. Understanding EOL software helps protect your business from security threats and downtime. Let’s explore how to navigate software’s inevitable end.
1. What is End of Life software?
End of Life (EOL) software refers to applications or operating systems that the vendor or developer has officially ceased to support. This means they will no longer provide updates, security patches, or technical assistance.
End of Life software meaning can be best understood by examining the typical software lifecycle. Software, like any product, progresses through distinct stages: development, release, maintenance, and finally, end of life. During the maintenance phase, vendors typically release updates to fix bugs, enhance features, and patch security vulnerabilities.

However, at a certain point, the vendor decides to discontinue support, marking the software’s EOL. This decision is often driven by factors such as the emergence of newer technologies, the high cost of maintaining older versions, or a shift in the vendor’s strategic focus.
The concept of software obsolescence is closely tied to EOL. As technology advances rapidly, older software can become outdated and incompatible with modern systems and security standards.
This obsolescence makes EOL software increasingly vulnerable to security threats and less efficient, ultimately posing significant risks to businesses that continue to rely on it.
Read more >>> Commercial Off-the-Shelf (COTS) Software | Definition, Benefit, Drawbacks
2. Understanding the implications
So, what happens when software reaches end of life? The transition from supported to unsupported status has significant repercussions. Understanding the risks of EOL software is crucial for any organization aiming to maintain a secure and efficient IT environment.
One of the most critical consequences is the increase in security vulnerabilities. EOL software becomes a prime target for cybercriminals without vendor-provided updates and patches. These systems are essentially left defenseless against newly discovered exploits, putting sensitive data and critical infrastructure at risk. The lack of updates and patches means known vulnerabilities remain unaddressed, creating open doors for malicious actors.
Furthermore, using EOL software can lead to compliance requirements issues. Many industries have strict regulations regarding data security and software compliance. Running unsupported software can violate these regulations, resulting in fines and legal repercussions.
The implications of using unsupported software extend beyond security; it can also lead to the potential for system instability. As EOL software ages, it may struggle to integrate with newer hardware and software, leading to crashes, errors, and performance degradation.
Let’s consider two prominent examples:
- Microsoft Windows XP:
When Microsoft ended support for Windows XP, millions of computers worldwide became vulnerable. Despite its widespread use, the lack of security updates made it a breeding ground for malware and cyberattacks. Many businesses and individuals faced security breaches and data loss due to their continued reliance on this EOL operating system.

- Adobe Flash Player:
Similarly, when Adobe Flash Player reached its EOL, it posed a significant security risk. Flash’s history of vulnerabilities, combined with the absence of further updates, made it a dangerous tool. Browsers and websites actively phased out Flash support, highlighting the necessity of transitioning away from EOL software.

These examples underscore the serious consequences of ignoring EOL software. The vulnerabilities, compliance issues, and instability create a hazardous environment for any organization.
Read more >>> What is Elixir Used For? 4 Benefits, 5 Frameworks
3. End of Life (EOL) vs. End of Support (EOS)
Navigating the complex world of software lifecycles requires a clear understanding of key terms, particularly the distinction between End of Life (EOL) and End of Support (EOS). While often used interchangeably, they represent distinct phases with different implications.
To truly grasp what does end of life mean for software, and to understand the difference between end of life and end of support in software, we need to delve deeper.
EOL vs EOS: The core difference lies in the breadth of cessation. End of Life (EOL) signifies the complete discontinuation of a software product. This means the vendor will no longer provide updates, patches, or support. The product is essentially retired.
End of Support (EOS), on the other hand, typically indicates a more specific cessation of technical assistance. While the vendor may still provide critical security updates for a limited time, they will no longer offer customer support, bug fixes, or feature enhancements.
Essentially, EOS is often a phase leading up to the final EOL.
To clarify:
EOL:
- Complete cessation of all updates and support.
- The product is considered obsolete.
- Significant security and compliance risks.
EOS:
- Cessation of most support, but potentially limited security updates.
- A transitional phase before EOL.
- Reduced support and increased security vulnerabilities.
The significance of these terms is directly tied to vendor support policies. Understanding the vendor’s stance on EOL and EOS is crucial for effective software lifecycle management. These policies dictate the timeline for support, the types of updates provided, and the overall trajectory of the software’s lifespan.
Recognizing these distinctions allows organizations to plan proactively, mitigate risks, and make informed decisions about software migration or replacement. Ignoring the difference between EOL and EOS can lead to unexpected vulnerabilities and disruptions, emphasizing the need for a thorough understanding of these critical terms.
Read more >>> What is Computer-aided Software Engineering (CASE)? | 10 Type of CASE
4. Best practices for managing EOL Software
Dealing with End of Life (EOL) software requires a strategic and proactive approach. To effectively manage these systems and minimize risks, organizations must implement robust end of life software best practices. These practices are integral to effective software lifecycle management, ensuring a smooth transition away from unsupported applications.
Best practices for managing end of life software begin with a thorough risk assessment and inventory. Identify all EOL software within your environment, evaluate the potential risks associated with each, and prioritize systems based on criticality. This inventory should include details about the software’s function, dependencies, and the data it handles.
While vendors no longer provide patch management and software updates for EOL systems, you can implement alternative strategies. Segmentation and isolation of EOL systems is crucial. By isolating these systems on a separate network segment, you limit their exposure to potential threats and prevent the spread of malware. This approach also allows you to implement stricter security controls around these isolated systems.
Virtualization or containerization can also be employed to encapsulate EOL software within a controlled environment. This approach can help maintain compatibility with newer systems and simplify management. However, it’s essential to remember that virtualization does not eliminate the inherent security risks of EOL software.
Ultimately, planning for migration or replacement is the most effective long-term strategy. Develop a roadmap for migrating to supported alternatives, prioritizing critical systems and applications. This plan should include timelines, resource allocation, and testing procedures.
Finally, implementing effective strategies to mitigate risks associated with EOL software requires a holistic approach. This includes:
- Regular security audits and vulnerability scanning.
- Implementing strict access controls and least privilege principles.
- Continuous monitoring of EOL systems for suspicious activity.
- Developing incident response plans specifically for EOL-related incidents.
By adopting these best practices, organizations can significantly reduce the risks associated with EOL software and ensure a more secure and stable IT environment.
5. Securing systems running EOL software
Even with the best planning, some organizations may find themselves temporarily needing to run End of Life (EOL) software. In these cases, it’s crucial to implement robust security measures to mitigate the inherent risks. Addressing how to secure systems running EOL software requires a multi-layered approach, focusing on minimizing exposure and detecting potential threats.
The primary concern with EOL software is its susceptibility to security vulnerabilities. Since vendors no longer provide updates or patches, these systems become easy targets for cyberattacks. Therefore, strengthening your IT infrastructure is paramount.
Here are key security strategies:
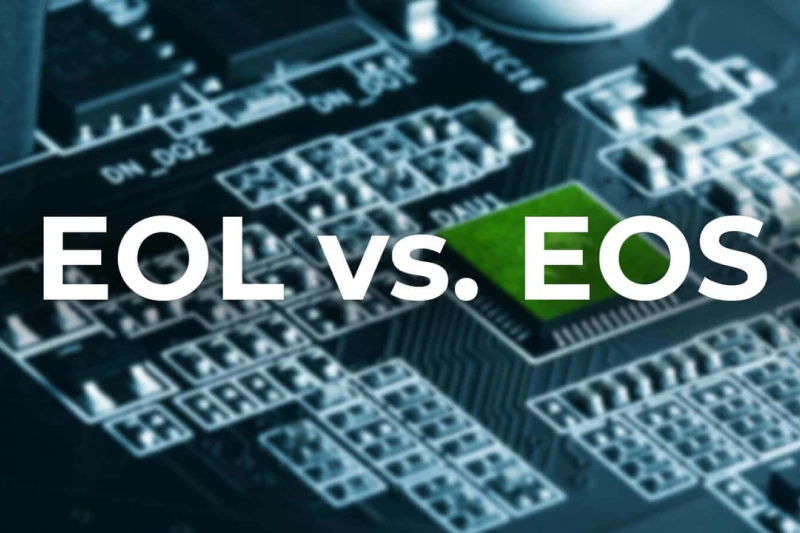
- Firewall and intrusion detection systems (IDS): Implement strict firewall rules to limit network traffic to and from EOL systems. Utilize IDS to detect and alert on suspicious activity, providing an early warning of potential breaches.
- Network segmentation: Isolate EOL systems on a separate network segment. This limits their exposure to the rest of your network and prevents the spread of malware in case of a breach. This is a critical practice for minimizing the blast radius of any security incident.
- Application whitelisting: Implement application whitelisting to allow only authorized applications to run on EOL systems. This can prevent the execution of malicious software and reduce the risk of infection.
- Enhanced monitoring and logging: Implement robust monitoring and logging solutions to track all activity on EOL systems. This includes logging network traffic, system events, and user activity. Regular analysis of these logs can help detect anomalies and identify potential security breaches.
- Virtualization and sandboxing: If possible, virtualize the EOL software and run it in a sandboxed environment. This adds an extra layer of isolation and can help contain the impact of any potential security incidents.
- Strict access controls: Implement the principle of least privilege. Limit user access to EOL systems to only those who absolutely require it. Use strong authentication methods, such as multi-factor authentication, to prevent unauthorized access.
- Regular vulnerability scanning: Even though patches are not available, regular vulnerability scanning can help identify known vulnerabilities in EOL software. This information can be used to implement compensating controls and further harden the systems.
By implementing these security measures, organizations can significantly reduce the risks associated with running EOL software, buying valuable time to implement long-term migration strategies.
6. The importance of proactive planning
In the ever-evolving landscape of technology, a reactive approach to software management is a recipe for disaster. This is especially true when dealing with End of Life (EOL) software. The key to mitigating risks and ensuring business continuity lies in proactive planning.
A comprehensive EOL strategy is not merely an IT checklist; it’s a critical component of overall business resilience. It requires a thorough understanding of your software inventory, risk assessment, and a clear roadmap for migration or replacement.
Waiting until a system fails or a security breach occurs is not an option. By anticipating EOL milestones, organizations can avoid costly disruptions and maintain a competitive edge.
IT professionals and business decision-makers play distinct yet interconnected roles in this process. IT professionals are responsible for the technical aspects: identifying EOL software, assessing vulnerabilities, implementing security measures, and executing migration plans.
On the other hand, business decision-makers are responsible for providing the necessary resources, aligning EOL strategies with business objectives, and ensuring that the organization’s overall risk posture is adequately managed. Collaboration between these two groups is essential for successful EOL management.
The long-term benefits of proper software lifecycle management extend far beyond avoiding immediate crises. When organizations tackle EOL problems in advance, they gain the ability to:
- Reduce security risks: Minimize exposure to vulnerabilities and protect sensitive data.
- Improve operational efficiency: Avoid system instability and downtime.
- Reduce costs: Prevent expensive emergency repairs and data recovery.
- Maintain compliance: Adhere to industry regulations and avoid legal penalties.
- Enhance business agility: Adapt to changing technology landscapes more effectively.
Investing time and resources in proactive EOL planning is not just about avoiding problems but building a robust and resilient IT infrastructure supporting long-term business success.
By embracing a proactive mindset, organizations can transform the challenges of EOL software into opportunities for innovation and growth.
7. The bottom lines
We’ve covered a thorough explanation of what is End of Life software, emphasizing its security and compliance risks. Understanding the difference between EOL and EOS, and implementing proactive strategies like risk assessments and migration plans, is essential. Securing EOL systems requires robust measures, including firewalls, network segmentation, and enhanced monitoring.
In today’s fast-paced tech environment, staying informed and proactive is paramount. We encourage you to assess your systems, develop a comprehensive EOL strategy, and prioritize software lifecycle management. By doing so, you’ll safeguard your organization.
For further insights into technology trends and best practices, follow Stepmedia.